IT documentation
without the invoice.
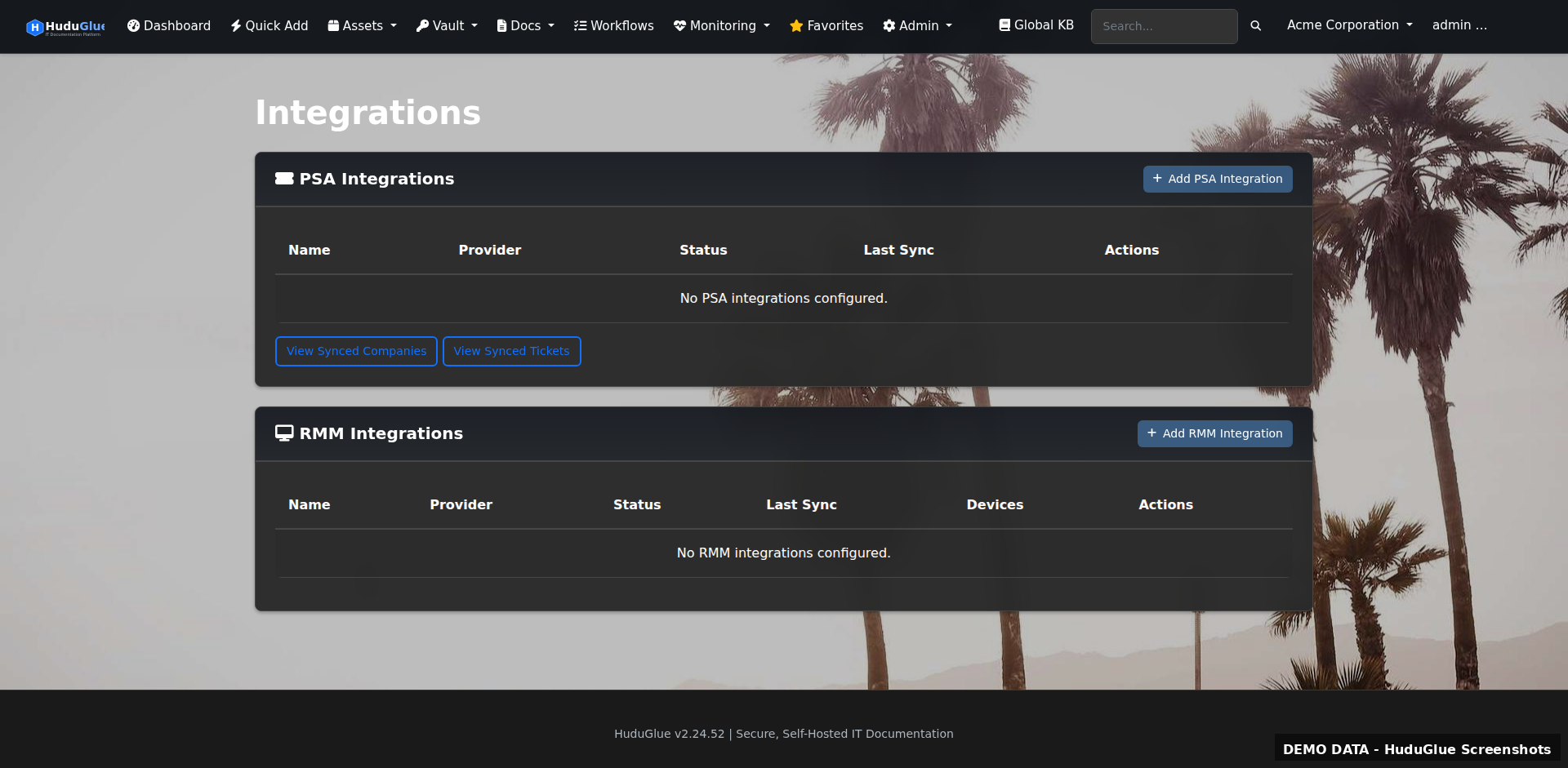
A full IT Glue replacement that runs on your hardware. AES-GCM encrypted vault, TOTP 2FA, 42 permission levels, 8 PSA integrations — no subscription, no vendor lock-in.
A full IT Glue replacement that runs on your hardware. AES-GCM encrypted vault, TOTP 2FA, 42 permission levels, 8 PSA integrations — no subscription, no vendor lock-in.
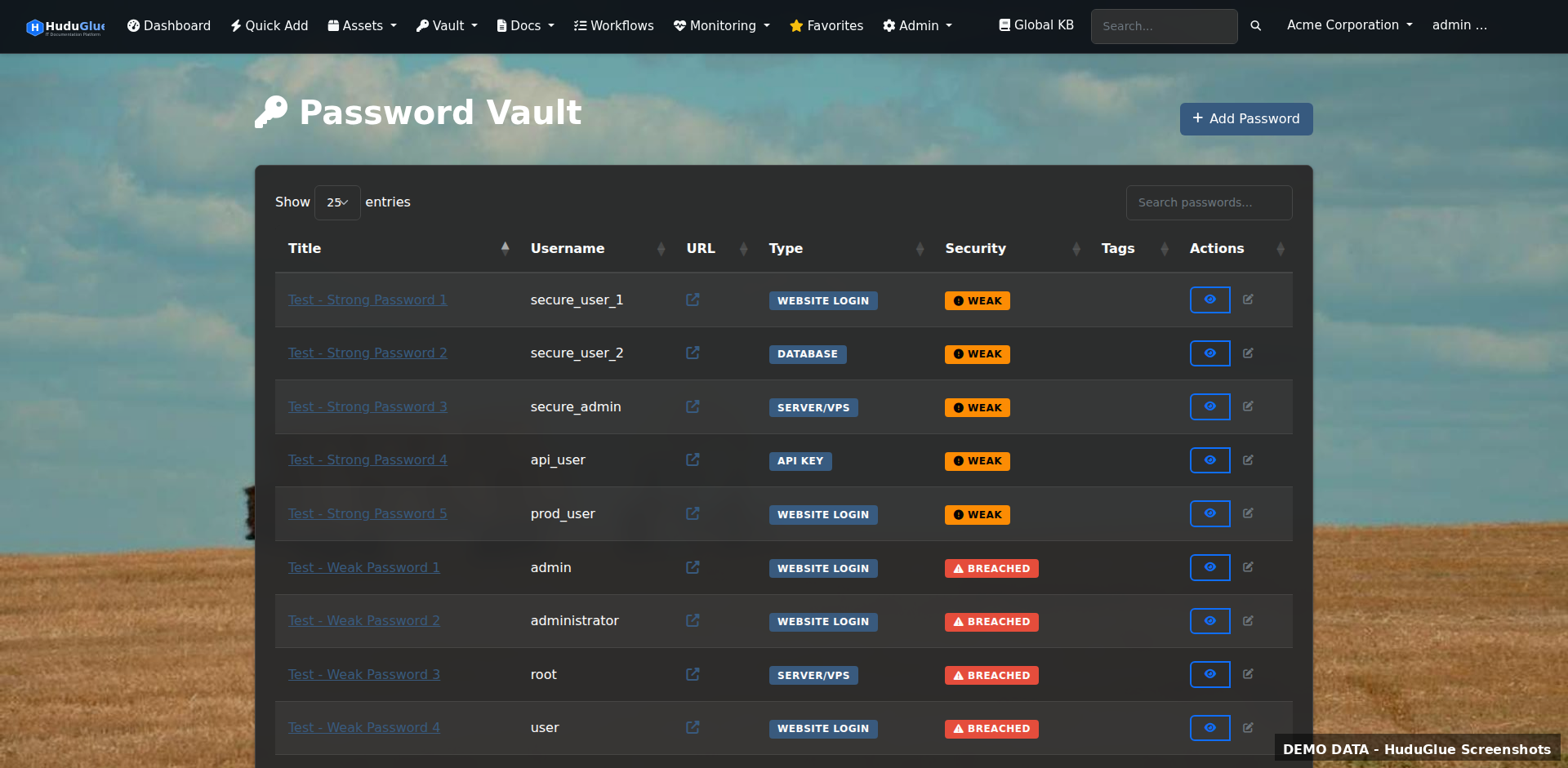
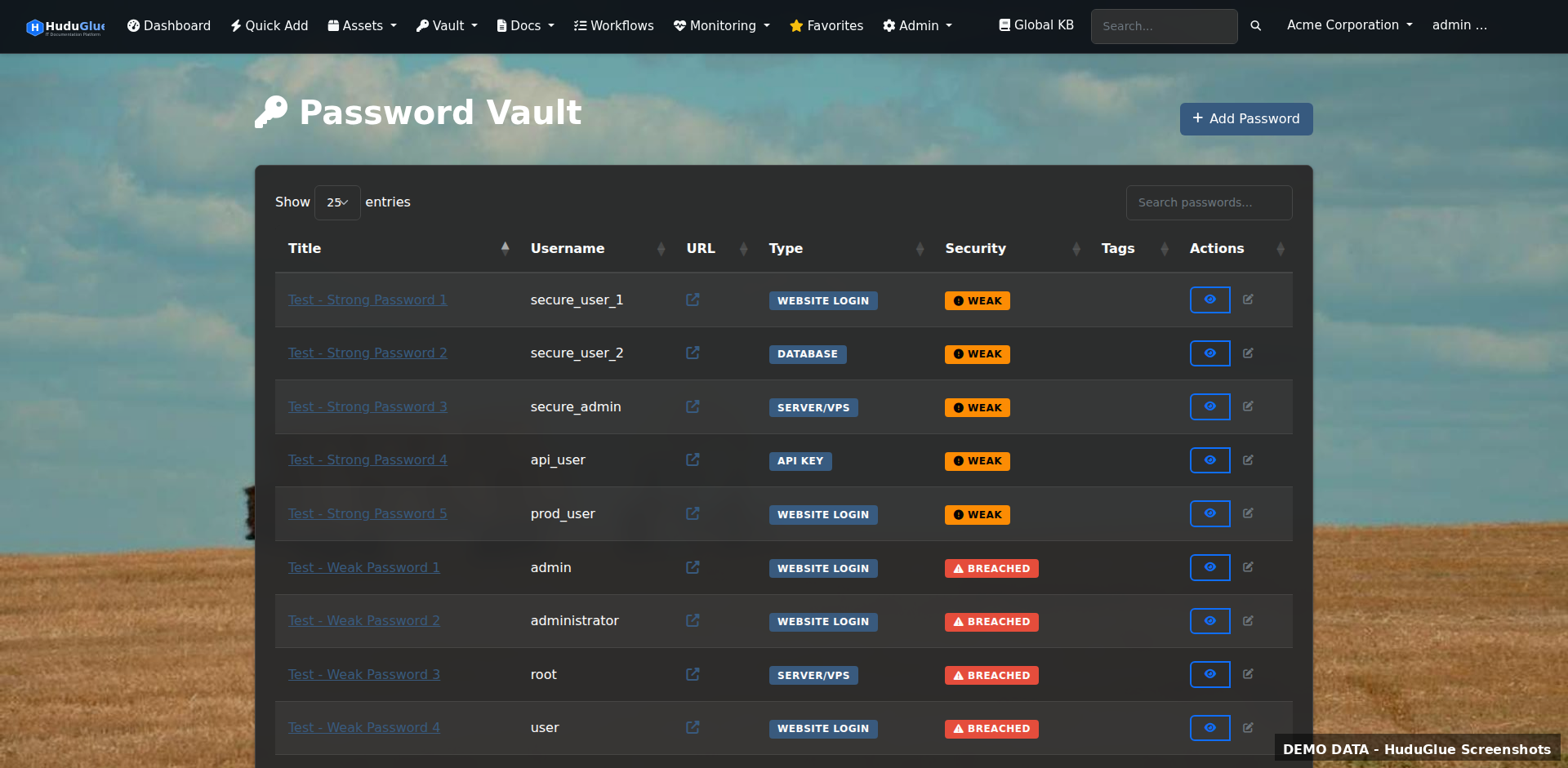
AES-GCM encrypted storage with per-record access control. Separate personal vault. Full audit log on every read. Your keys stay on your server.
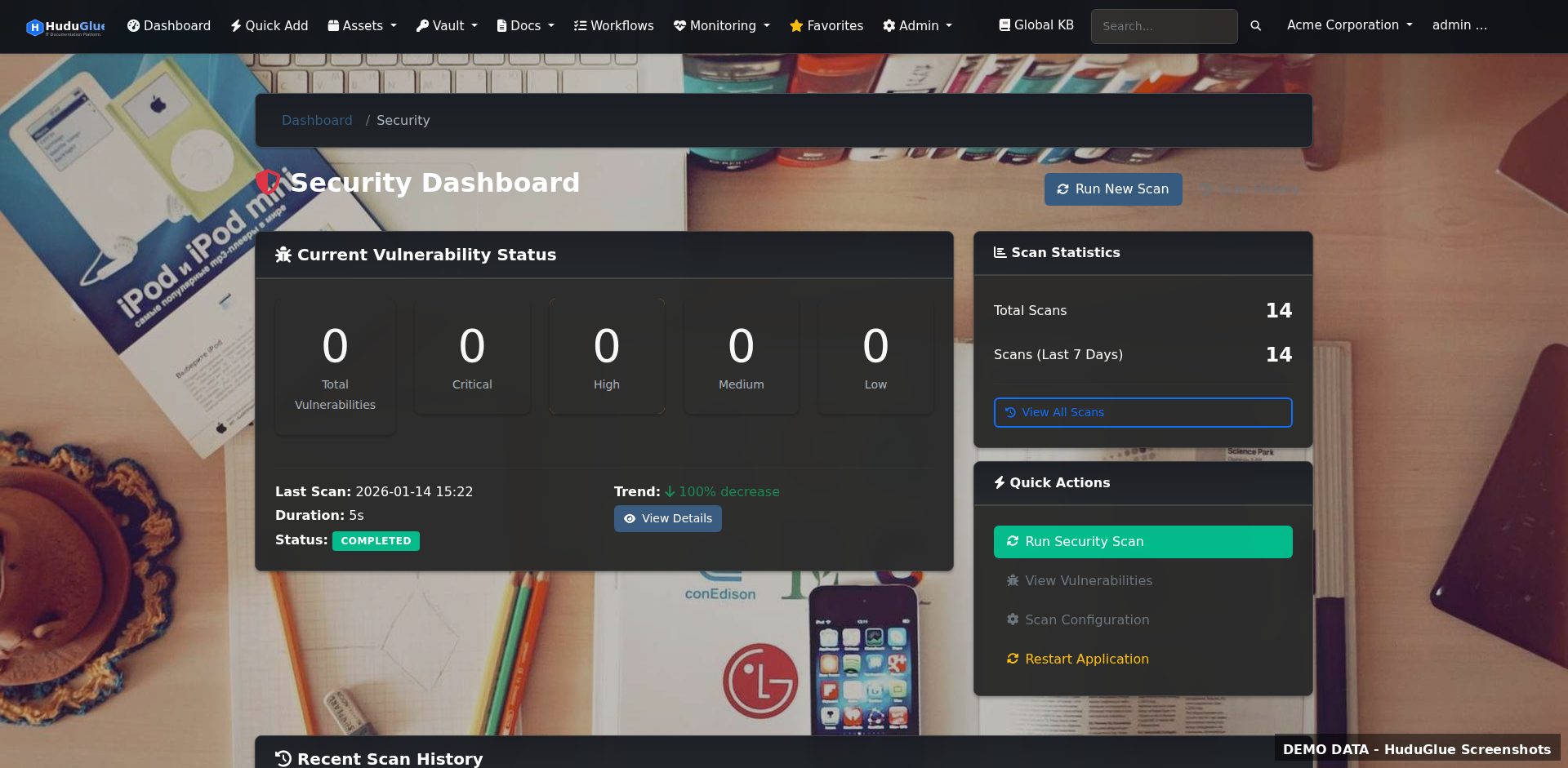
Continuous vulnerability scanning with Snyk integration, OS package security checks across your fleet, SSL certificate expiration tracking, and website uptime monitoring — built in, not bolted on.
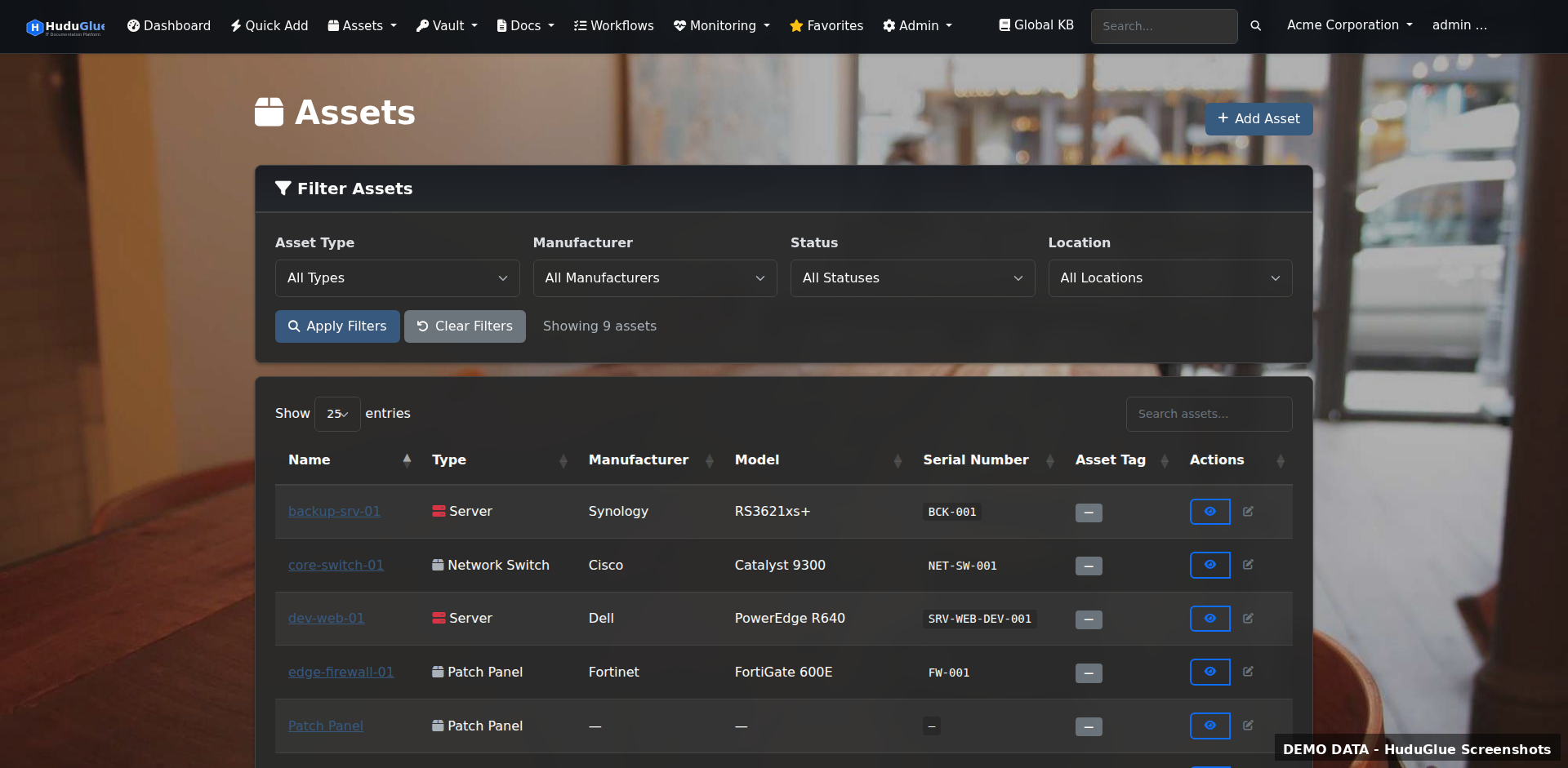
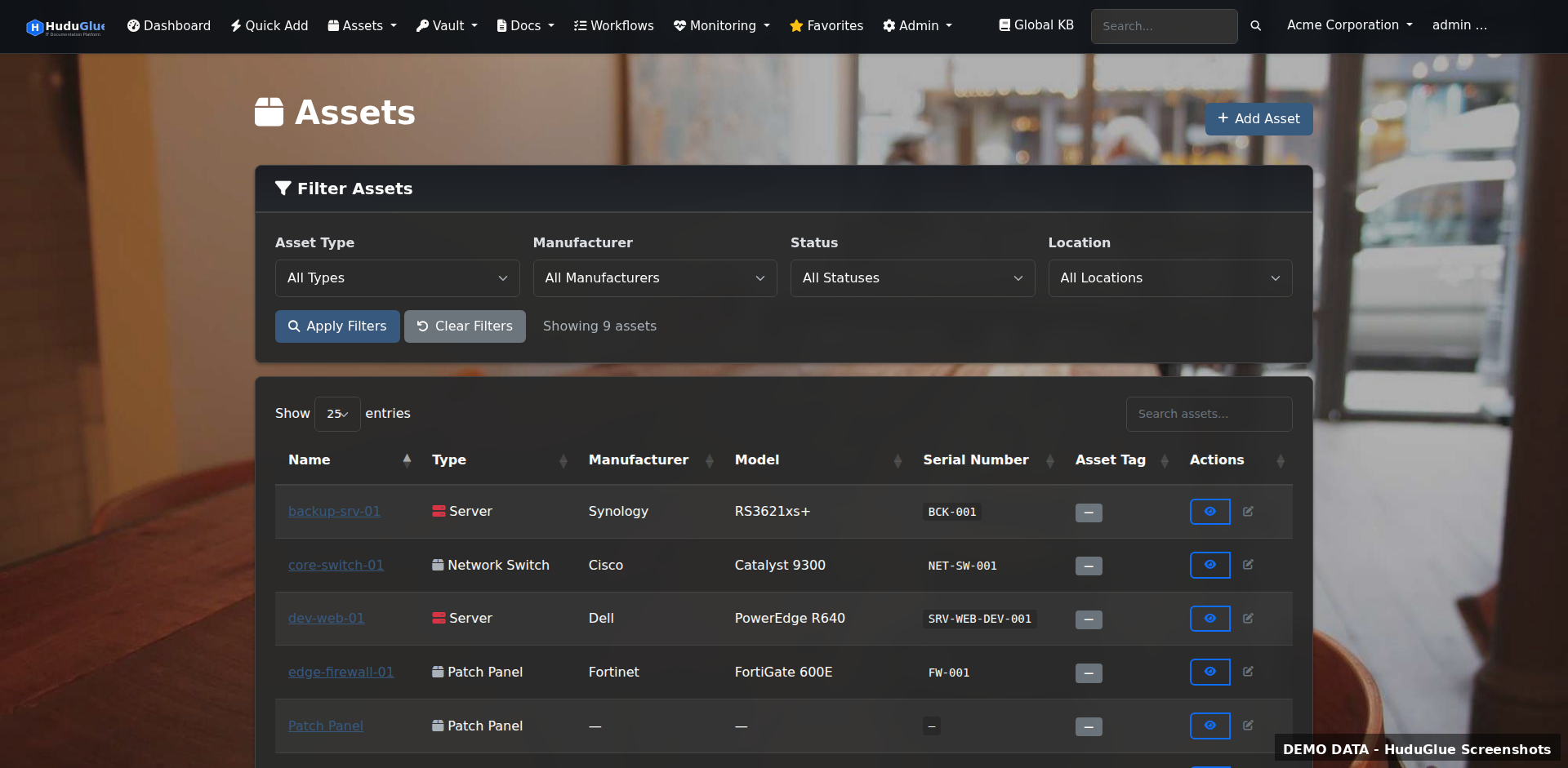
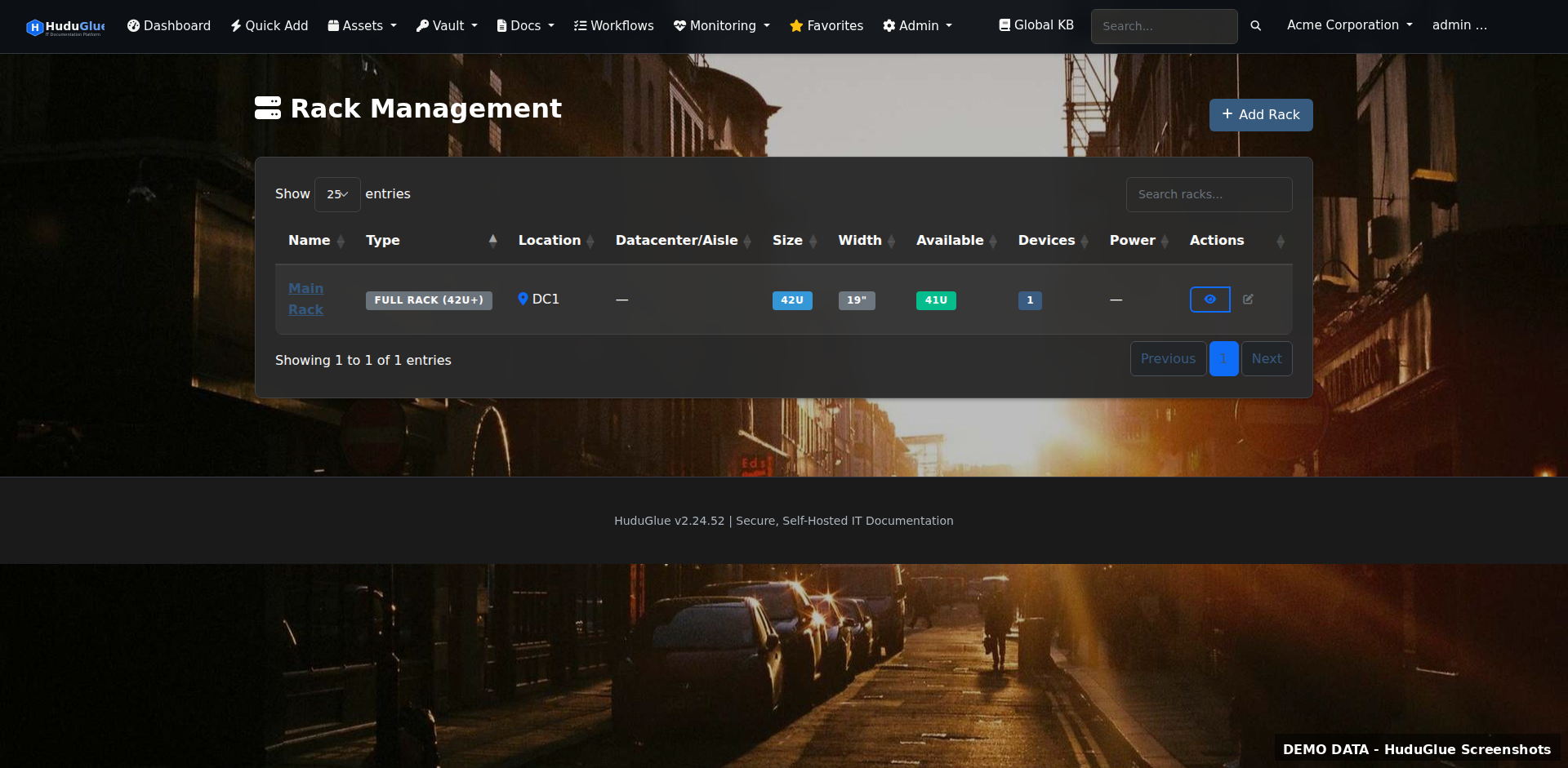
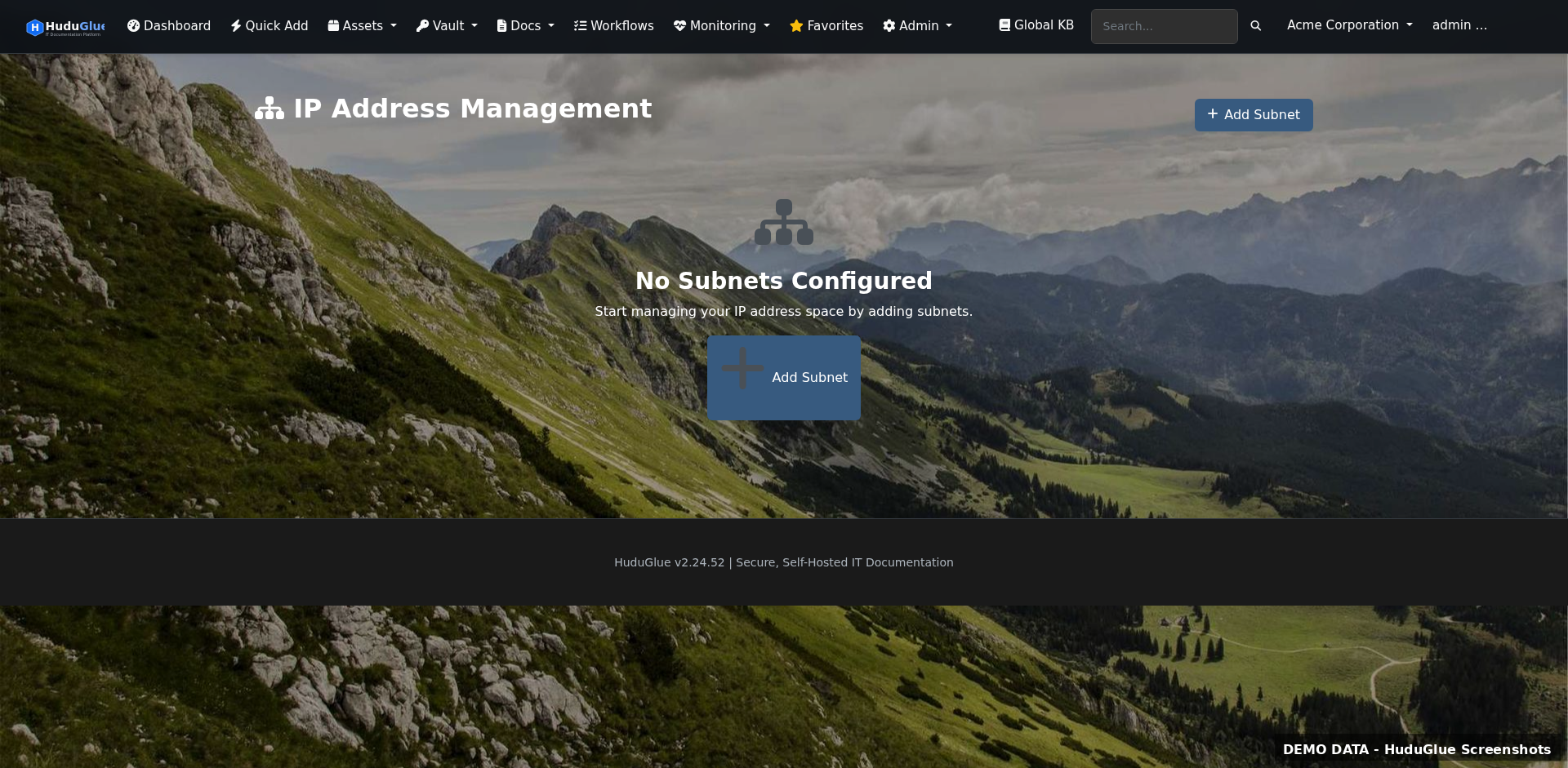
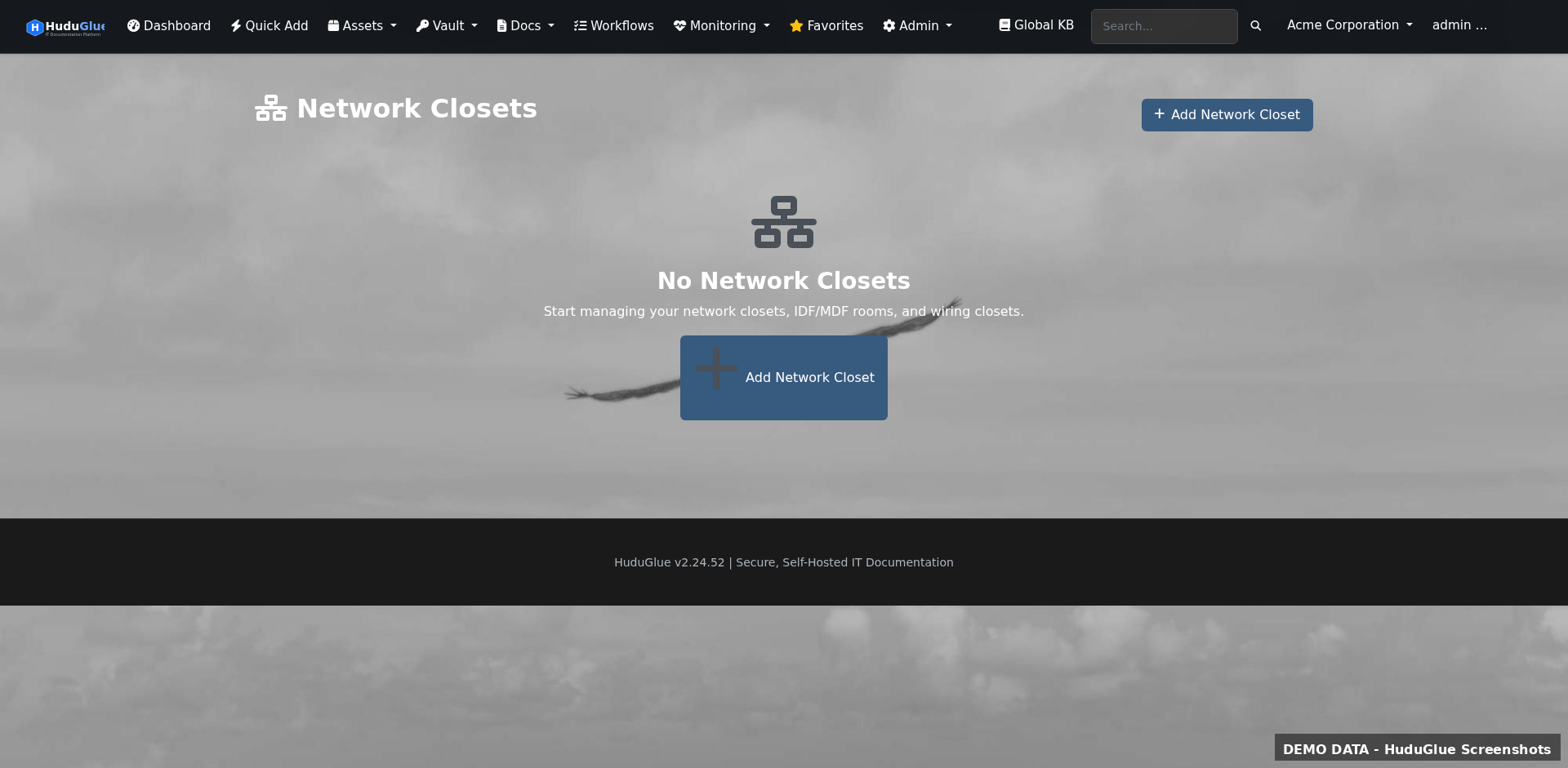
Comprehensive asset tracking from the rack to the endpoint. Network discovery via nmap, IPAM with subnet visualization, VLAN management, and patch panel mapping — all linked to your client organizations.
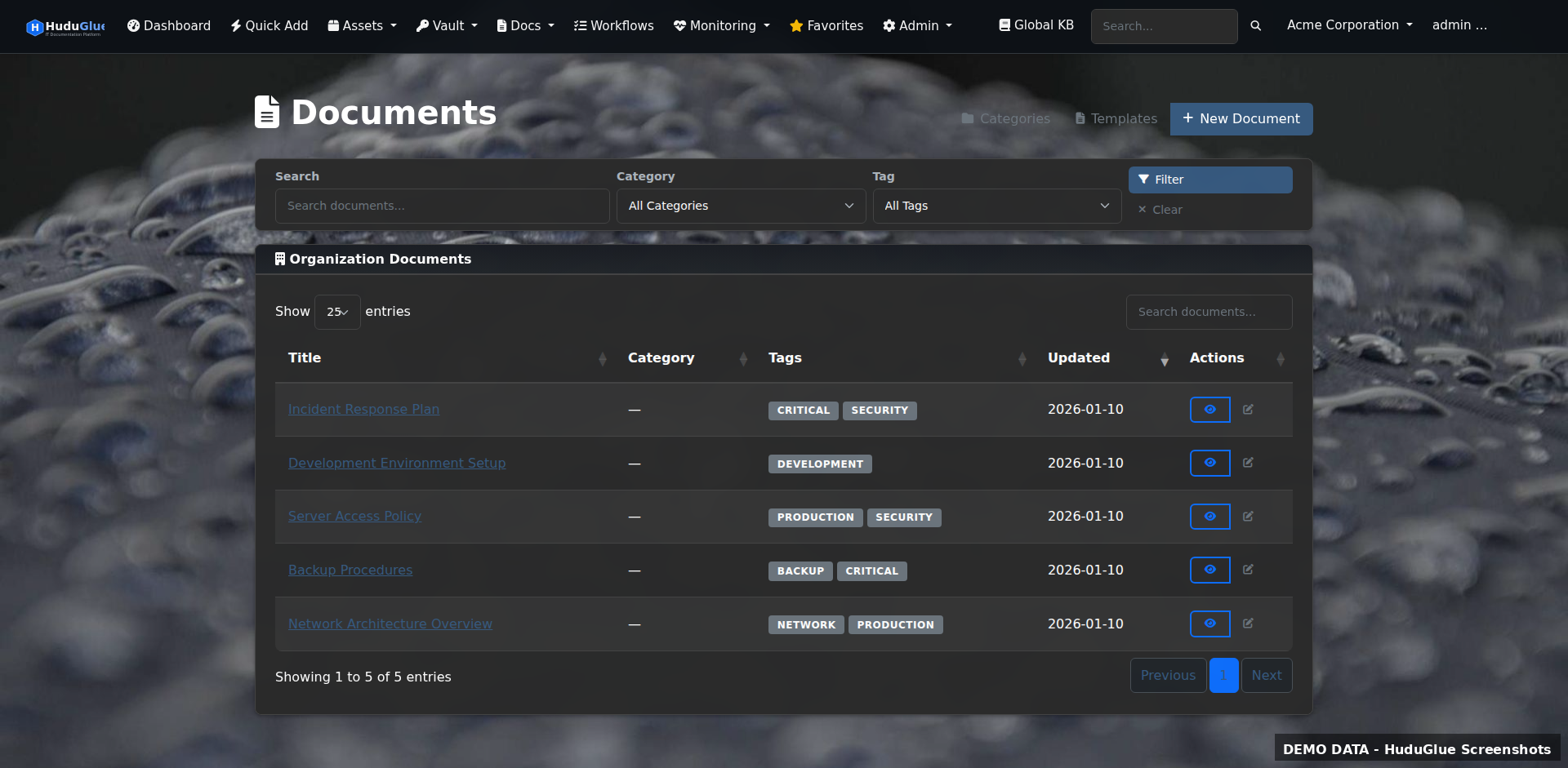
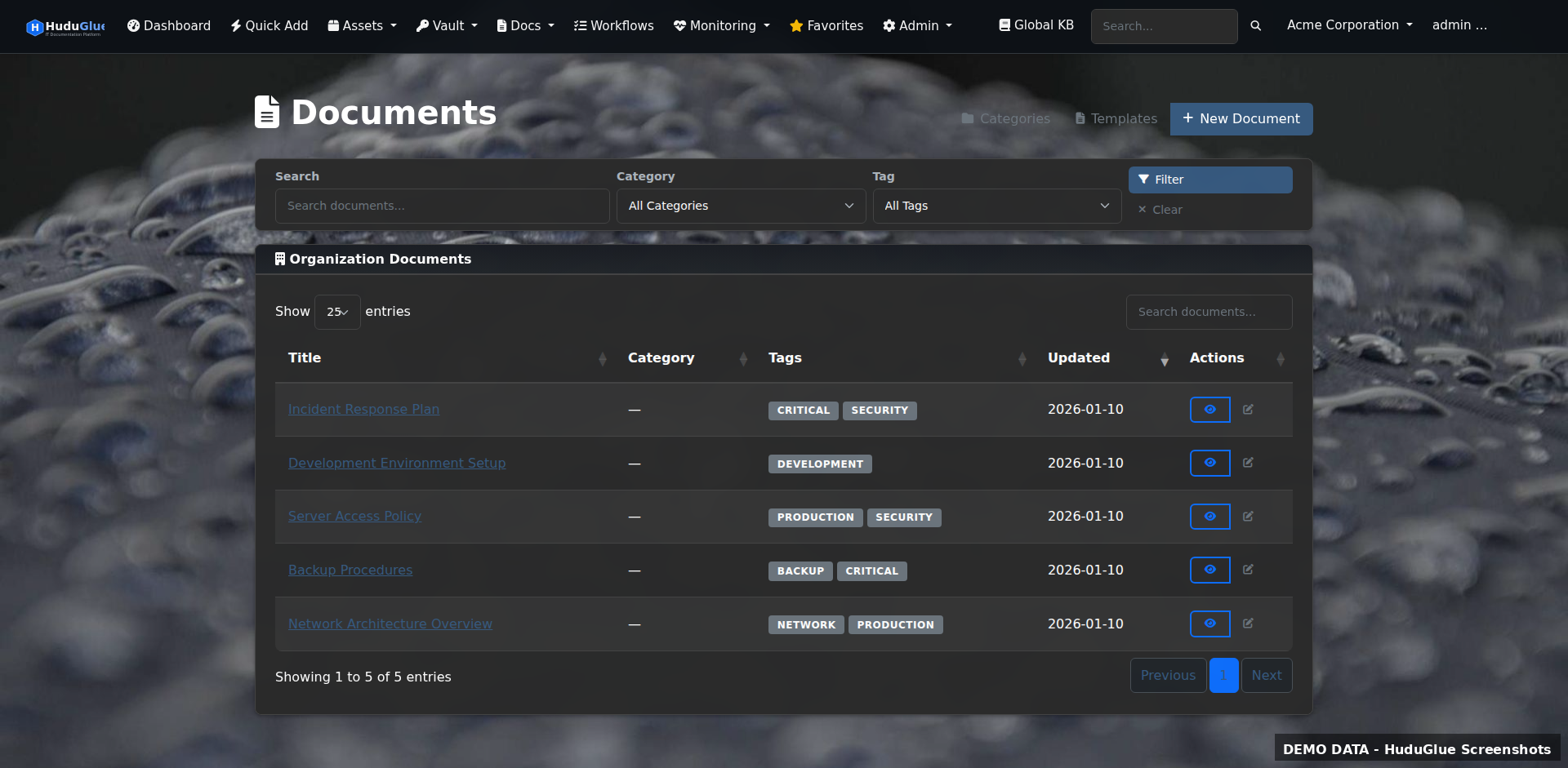
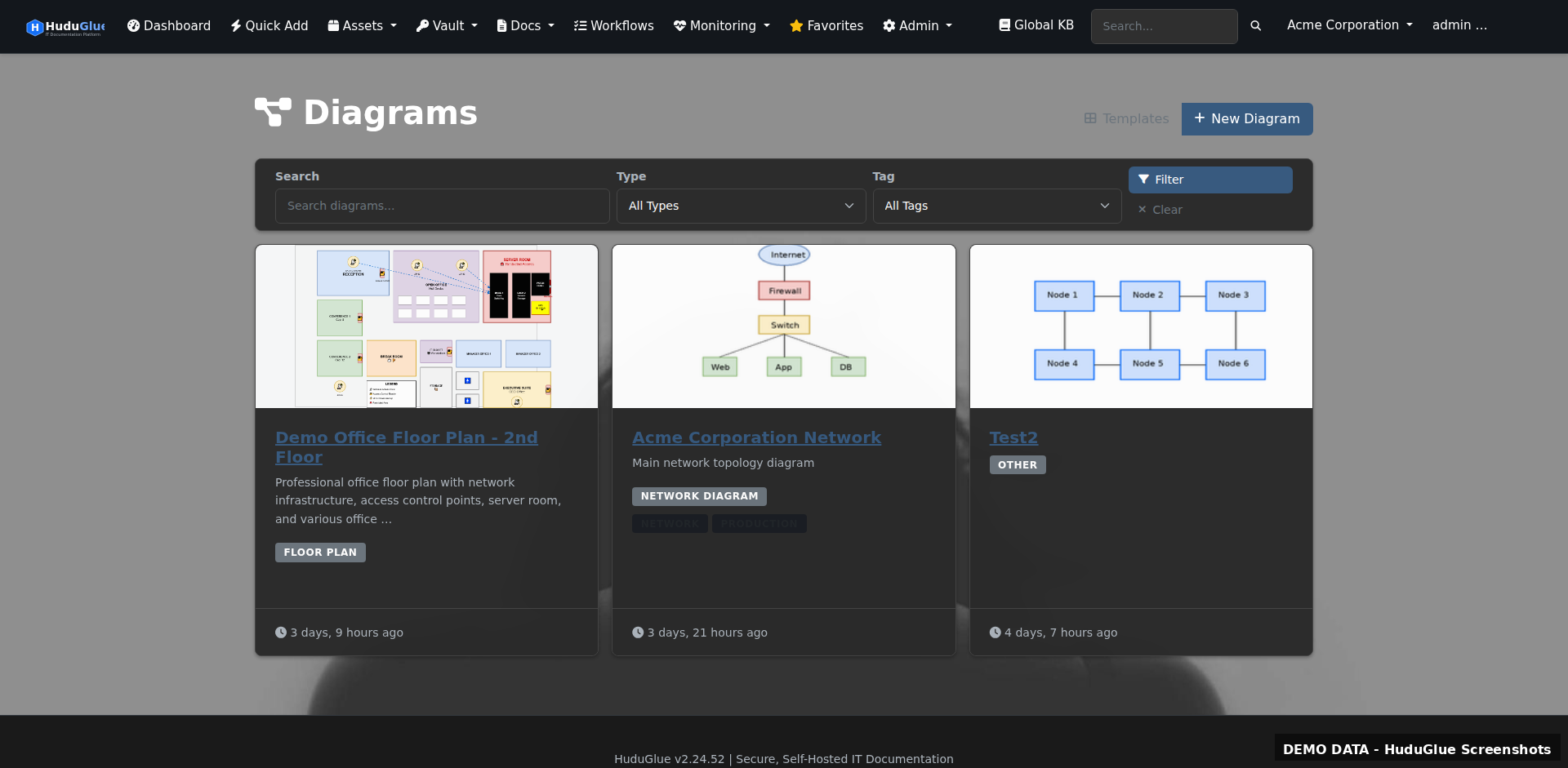
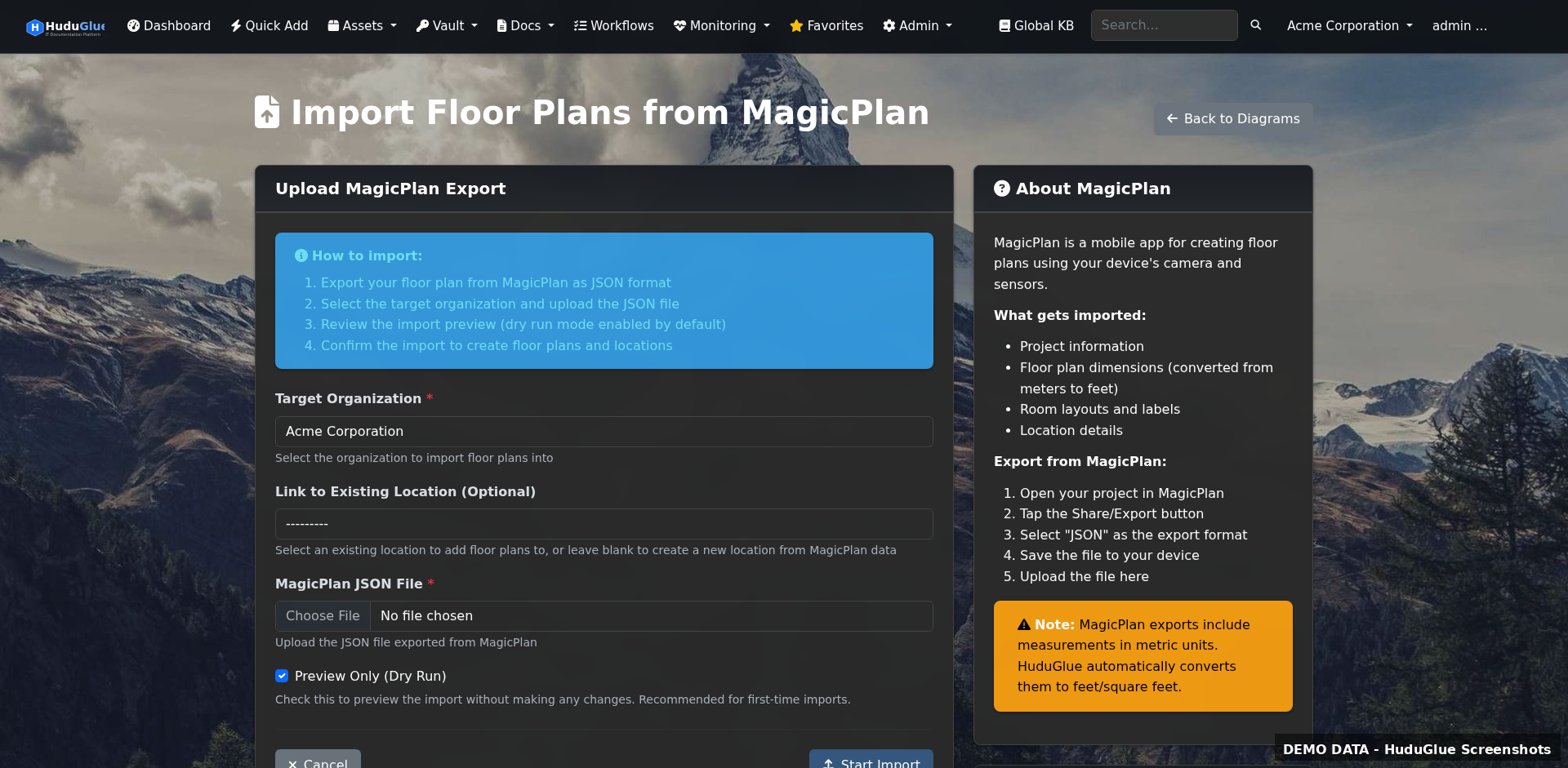
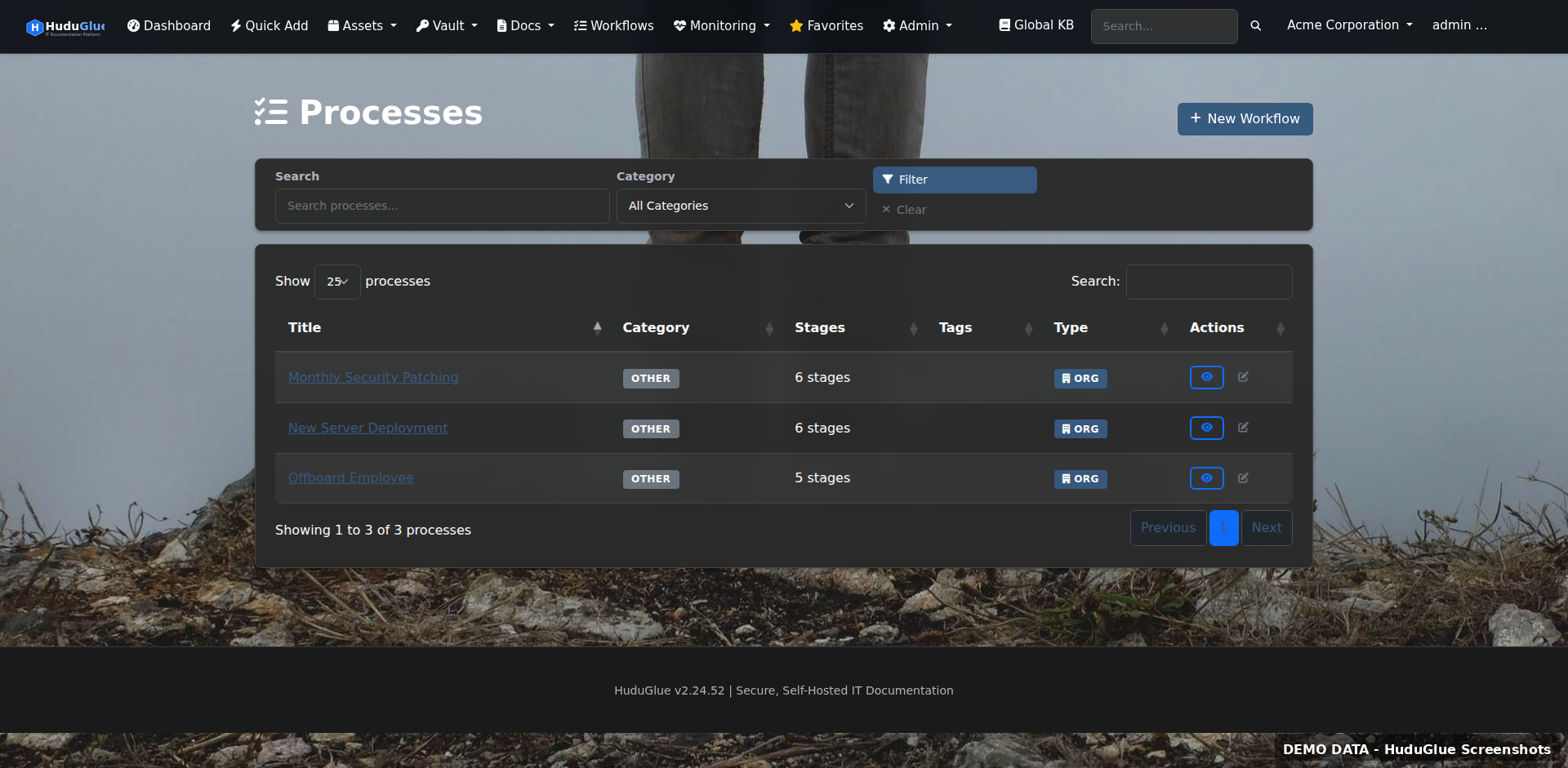
A real knowledge base with version history, embedded Draw.io network diagrams, MagicPlan floor plan imports, and workflow automation. Everything your techs need, organized by client.
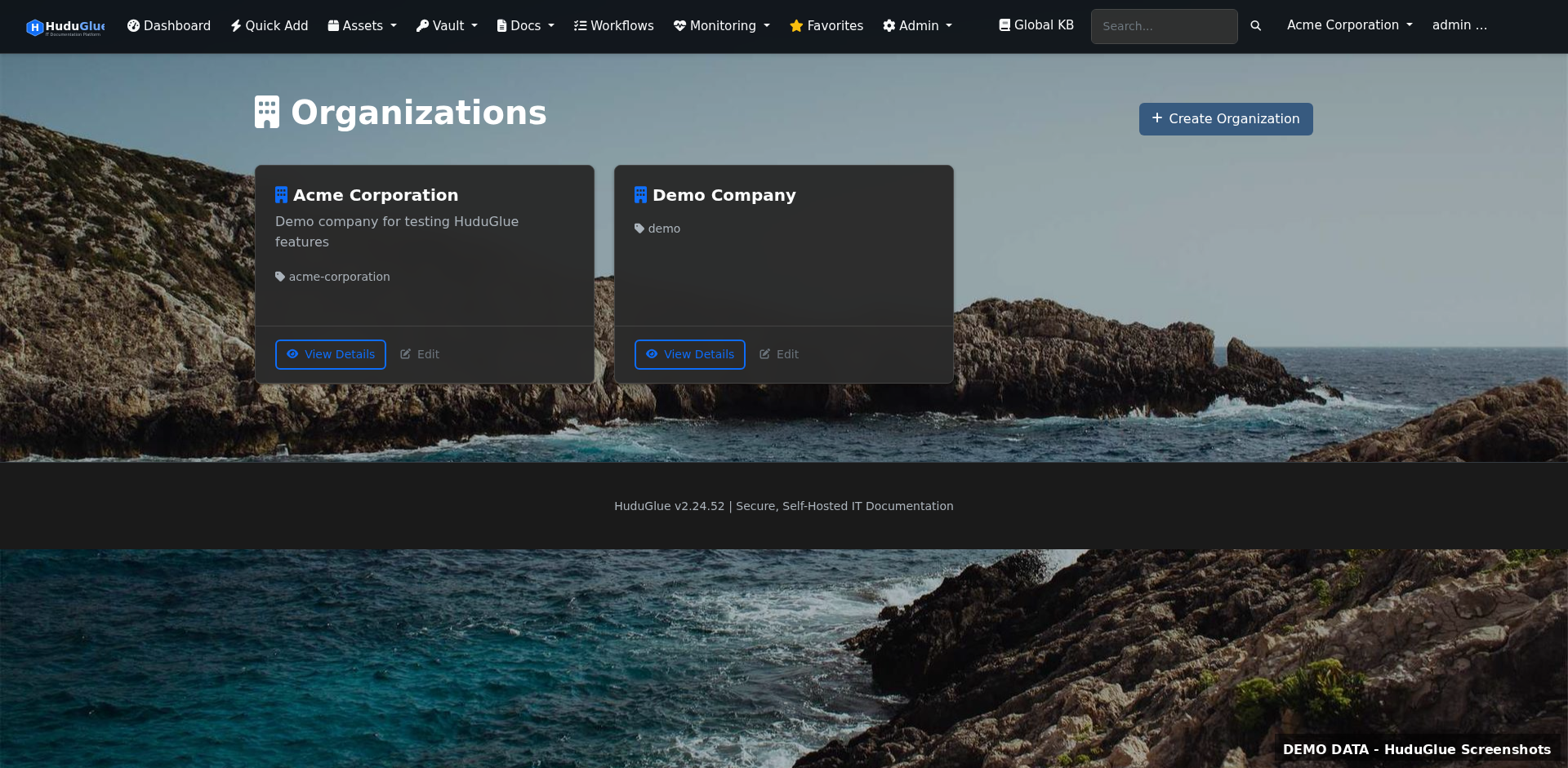
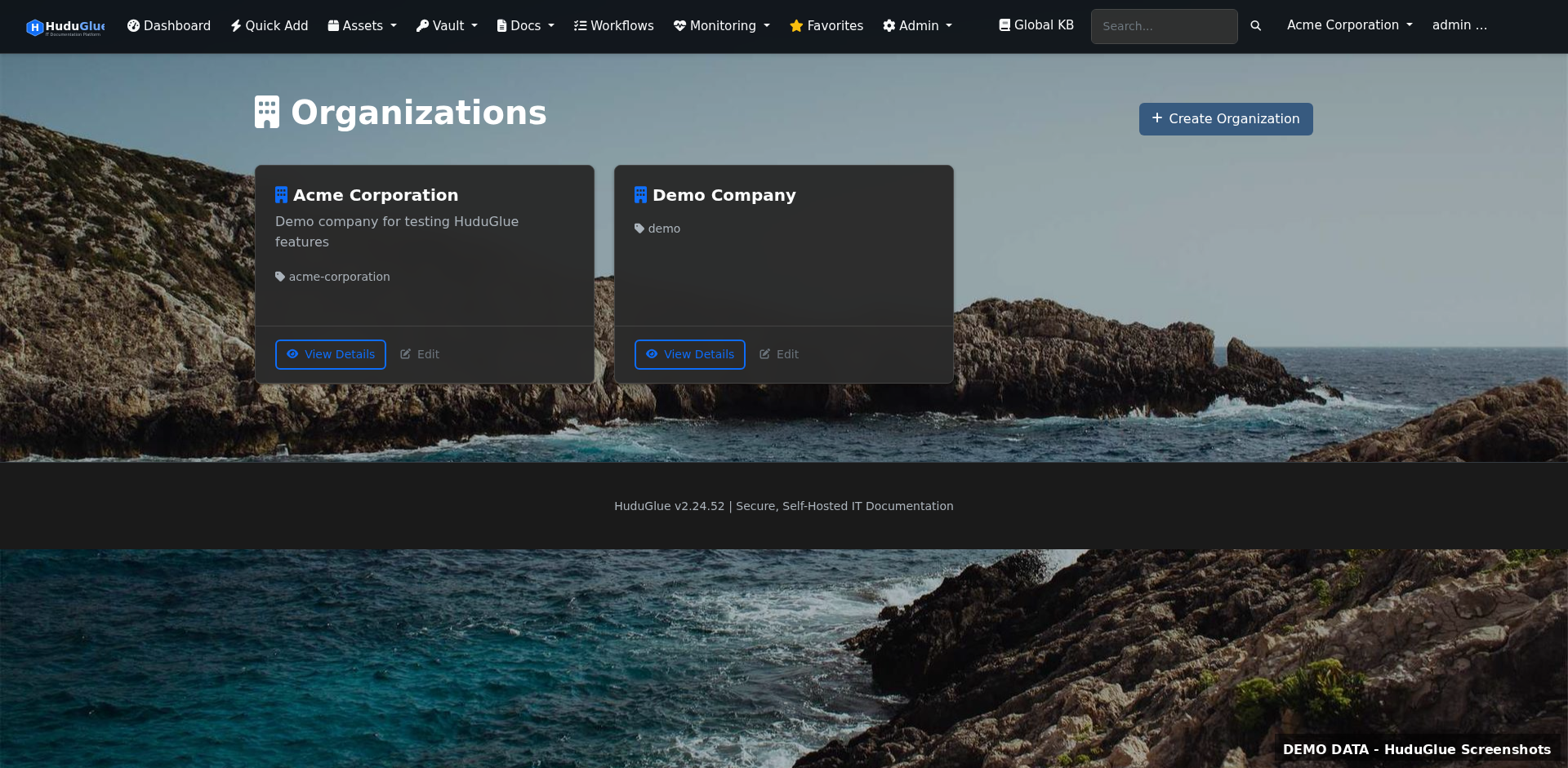
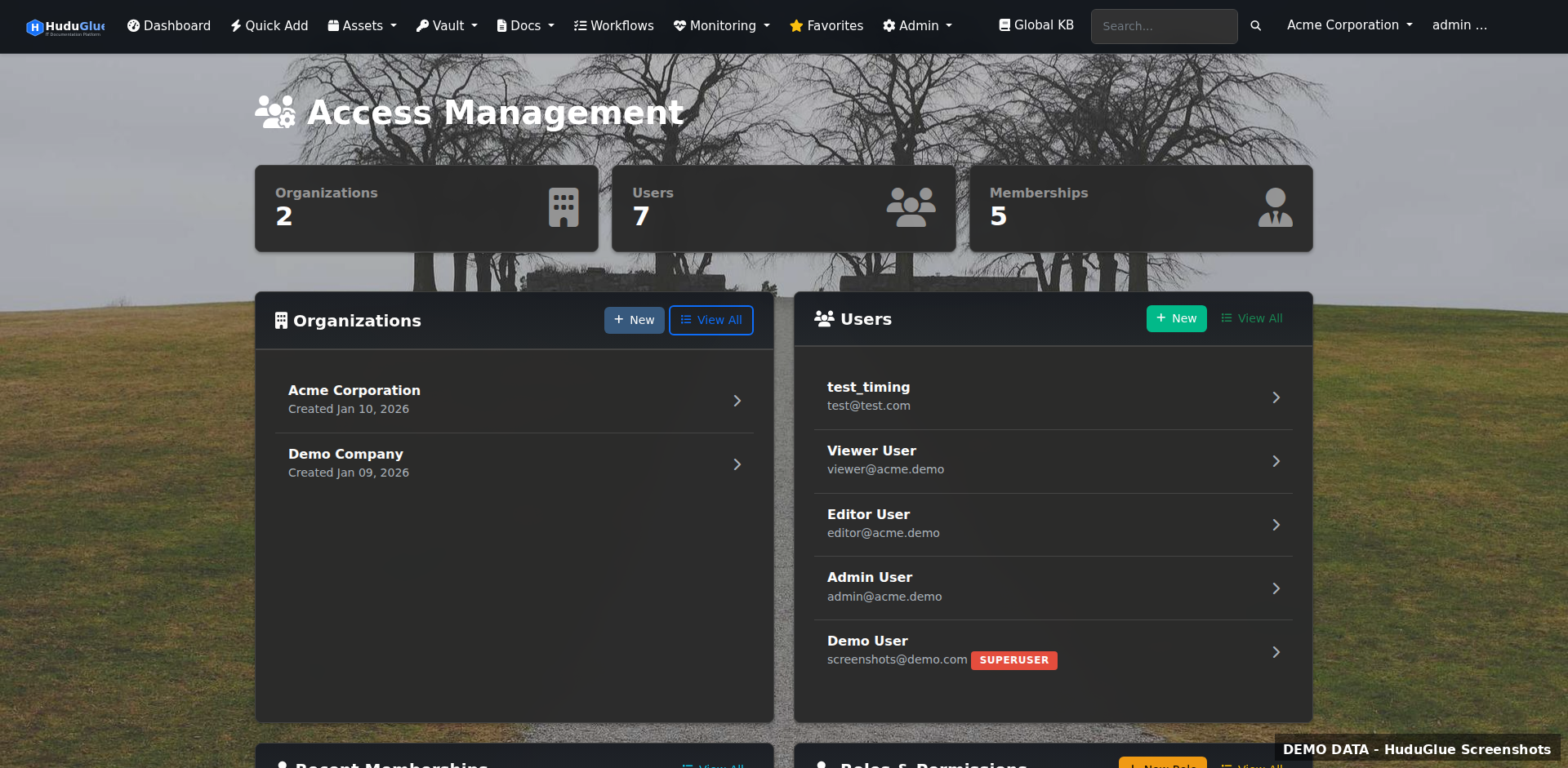
Full multi-organization support with per-org data isolation, granular permission sets, and role-based access down to individual records. Built for MSPs managing dozens of clients under one roof.
A mature, fully-built product — not a prototype.
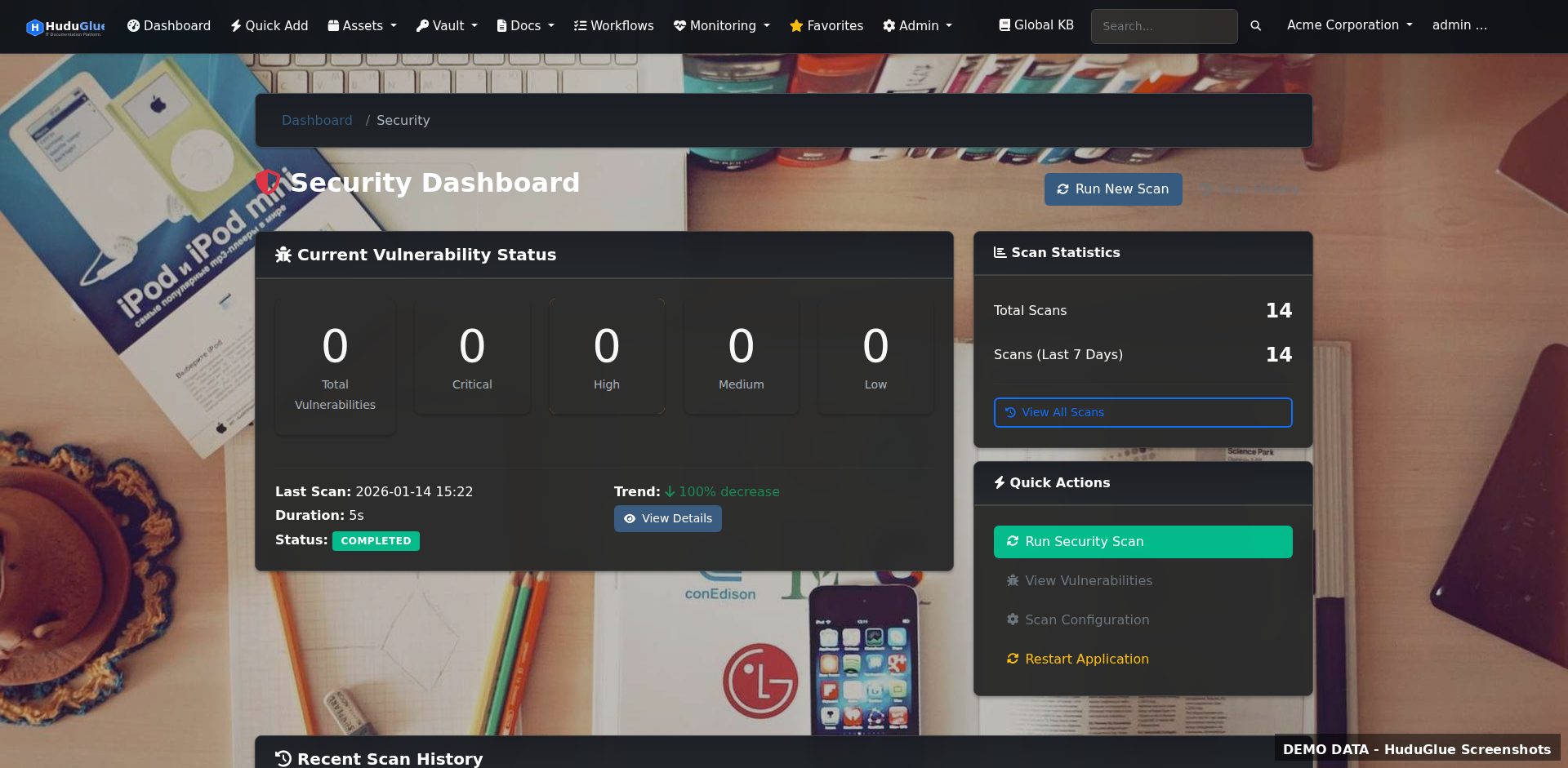
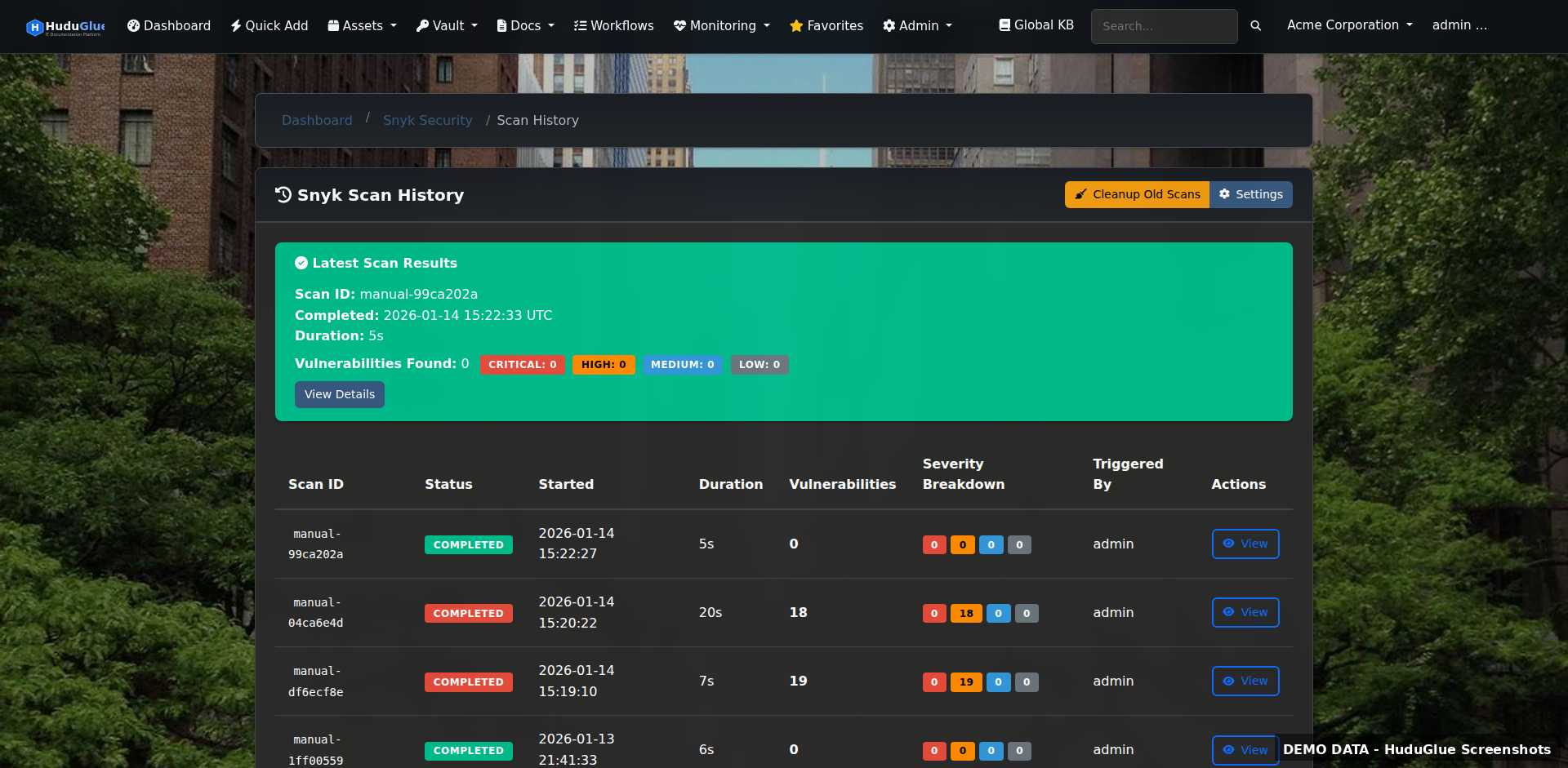
We use ExploitHound — our internal security intelligence and vulnerability correlation platform — alongside other scanning tools and review processes to identify CVEs, suspicious behavior, exposed services, and potential risks before they become bigger problems.
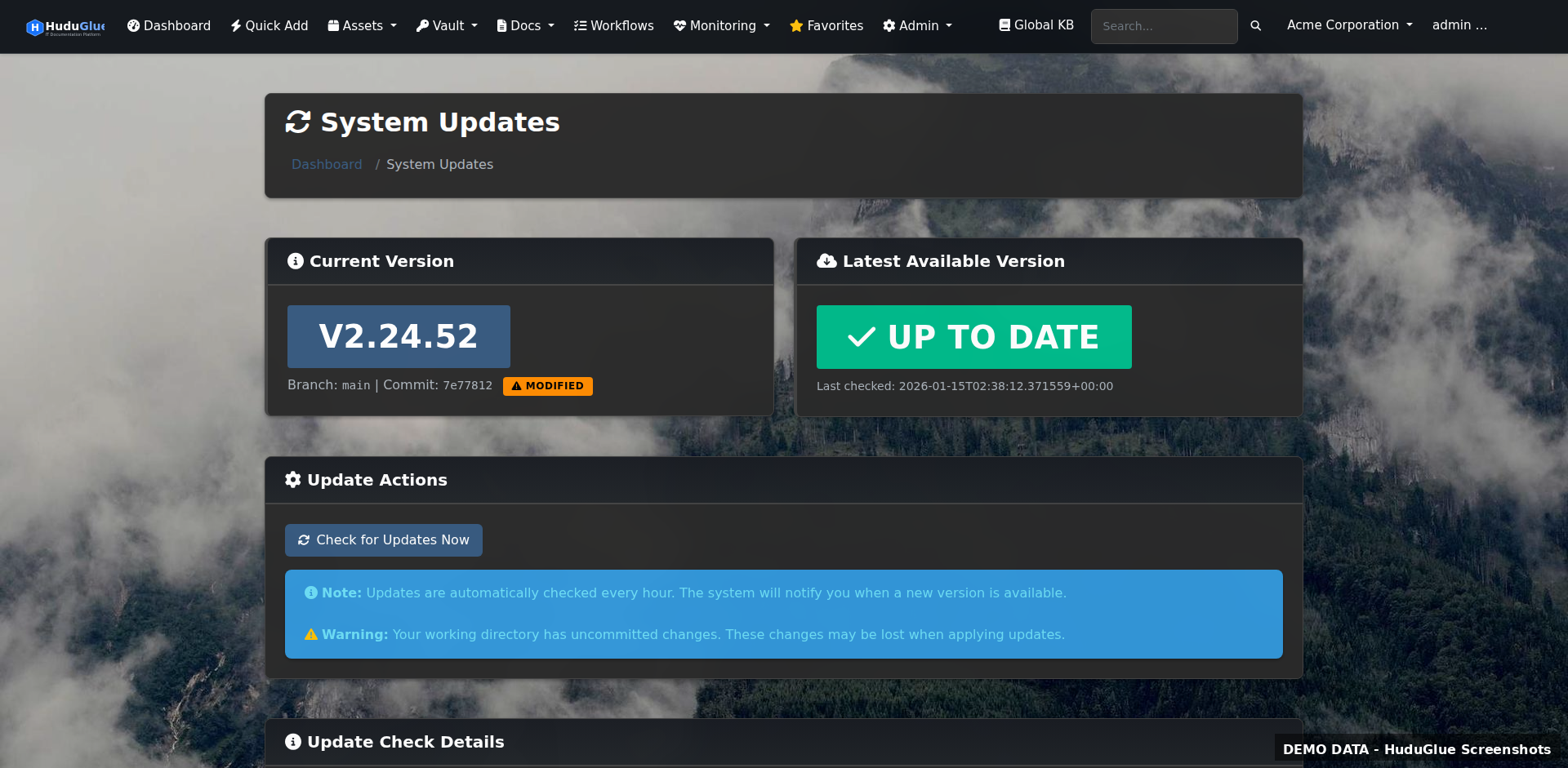
exploithound.com →Deploy on your hardware in under an hour. One-click web-based updates. No phone home, no telemetry, no lock-in.